Nowadays, people are quite reliant on their gadgets in order to survive. Unfortunately, as more people have access to these things, it becomes more likely that their gadgets can be stolen. Having that happen can leave someone compromised, especially if there was important data on that gadget.
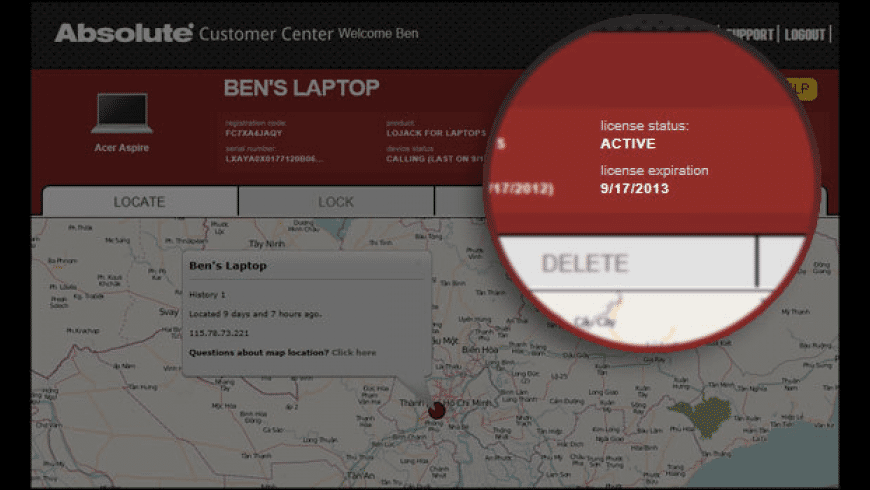
You may also can read consumer evaluations on NEW “Lojack For Laptops Premium 3 Year Mac”. Purchasing “Lojack For Laptops Premium 3 Year Mac” with us, We assure 100% customer satisfaction. Whilst the price tag may well seem higher, you can get your “Lojack For Laptops Premium 3 Year Mac” on sale at a fantastic Check Price here. This Premium version will protect your computer for up to 3 years. Systems requirements include Mac OS X v10.4 or higher and an internet connection. Without LoJack for Laptops, the odds of recovering a stolen laptop are about 3%. LoJack for Laptops has returned over 27,000 laptops to their rightful owners. Stay protected, and keep your data safe.
Related:
Hi, I just spent a fourtune on a new mac and peripherals, and will be buying another one next month for my business. I really want to find a way to help protect my investment from theft. I've seen ads for stuff that is like a lojack for computer laptops. FindMyMac can send a beep or message to the lost Mac screen, Lock the Mac and erase the content. Unfortunately, these features are not enough to retrieve your mac if you lost it. Hence, a greater share, as per the FBI, 97% failed to recover their stolen Mac. Sounds upsetting, but the truth is if your Mac is gone, it is surely a goner.

However, as these things become more likely, so do the means to counteract it. If you have had a gadget stolen, you may have tried to use Computer Tracking Softwareto see if you could still locate it. With software like these, you can have access to tools that let you locate your gadgets in the event they get lost or stolen.
Tracking Devices & Data Recovery
My Laptop Tracker
VT Explorer For Windows
YoYo Laptop Tracking Software
LoJack For Laptops
There are software that can help you find any of your portable gadgets if they should happen to get lost, not just a laptop. Mobile Tracking Softwarecan help you find these these items if they do go missing. These software can especially help you if it was your phone that went missing. In the case of a phone, you could have a lot of information there that could be compromised if stolen, such as contact and personal information, personal notes, etc.
- Tracking reports – As long as you have the apps installed, you can receive regular reports from your device for as long as it is connected to the Internet. Your device can tell you where it is, which would make it easier for you to tell the authorities.
- Screen captures – The camera on your device can secretly take screenshots of the area around it, and possibly the culprits as well. Having photos of the vicinity can make it easier to locate where your device is, through analysis of the details in the photo.
- Remote lock and delete – For the purpose of safety, you can remotely tell your device to lock itself, preventing thieves from accessing your data. You can also go a step further and have the device wipe the data, if you think the data could be accessed anyway.
- Data recovery – If you have had to delete your data, you also have resources to recover the data, so that you will lose nothing. If you have another device, you can download your important data there.
Unistal Laptop Tracking Software
LAlarm
LockItTight
CyberTracker – Most Popular Software
If some of your more important data are in the form of documents, you may want to use software that can keep your documents organized. These software can also keep a record if anyone should open your documents and when. These Document Tracking Softwareallow you to keep track of all your documents, even if your device should be stolen. You will be able to receive reports if your documents are accessed by a compromised device, and react. Software like these should be able to help you protect whatever important data you have on your devices so that it should be harder to compromise your data. And in the worst case, you always have the option of deleting the data to ensure that it cannot be read.
Try out the software we have lined up for you and see which of them you prefer. It’s always better to be safe than sorry.
Related Posts

All editions of Absolute are built with Persistence™ Technology
See all devices, on and off your network, and collect hundreds of hardware, software, security status, usage, and geolocation data points automatically, with 365 days of historical logs.
- Customizable dashboard, reports and alerts
- Measure device usage
- Automate hardware inventory
- Monitor installed software
- Assess security posture
- Monitor application health
Detect when your endpoints enter an unauthorized area, and take remote action to remediate endpoints risks immediately by rendering devices useless or deleting the data they contain.
All Absolute Visibility features- Detect unauthorized device movement
- Remote device freeze, on-demand or with offline timer
- Full or selective data delete
- Enable firmware protection
Establish resilient security by ensuring your critical apps remain active at all times. Remotely identify sensitive data, track web usage, gather precise insights or remediate endpoint vulnerabilities, and investigate stolen devices.
All Absolute Control features- Make critical applications self-healing
- Remotely scan for sensitive information
- Run PowerShell or BASH scripts on any device
- Track usage of web tools or content
- Investigate and recover stolen devices
Absolute Console
Cloud-based console, centralized dashboard, customizable widgets, pre-defined and customized reports and alerts, role-based access control, single sign-on, 2-factor authentication
Track Hardware
Report and alert on hundreds of hardware attributes, pre-built and custom reports, track new device activations and connection history, track the evolution of offline devices, flag missing devices and be alerted when they connect to the internet, track device location with 365 days of history
Measure Device Usage
Assess device usage based on device interaction events, report on daily average usage by device, and compare usage across different device groups to detect underutilized devices
Monitor Installed Software
Assess installed software on your devices to identify possible license non-compliance or waste, vulnerable apps or versions, policy non-compliance, and shadow IT or new user needs
Assess Security Posture
Report on encryption and anti-malware status across your device population, monitor evolution of encryption status over time
Monitor Health of Critical Applications 2
Report on the health status of critical applications, such as Endpoint Management, VPN, Endpoint Protection, or Data Protection
3rd-party Integrations
Integration with ServiceNow and SIEM tools
Detect Unauthorized Device Movement
Define geofences to detect unauthorized device movement and be alerted when a device crosses a geofence
Remotely Freeze Devices
Freeze a device with custom message - scheduled or on demand, set an offline timer to automatically freeze devices
Remotely Delete Data
Selectively delete files on any device, and perform an end-of-life device wipe with compliance certificate
Enable Firmware Protection 3
Create, remove, or change supervisor password remotely and at scale
Make Critical Applications Self-healing 2
Enable resilient endpoint security, by automatically repairing and reinstalling critical applications, such as Endpoint Management, VPN, Endpoint Protection, Data Protection, when they are found to be missing, disabled, or not running in a healthy state
Identify Sensitive Information on Devices
Discover PII, PHI, PFI, SSN, GDPR data and Intellectual Property on/off network, assess data risk, estimate cost of exposure, identify devices with sensitive files syncing with cloud storage (Dropbox, iCloud, Box, OneDrive)
Remotely Query & Remediate Devices at Scale
Leverage 130+ pre-built workflows from the Reach Library, and run any custom PowerShell or BASH script on one or multiple devices
Investigate and Recover Stolen Devices
Leverage the expert Absolute Investigations team to investigate and recover stolen devices in collaboration with law enforcement (Service Guarantee for unrecovered devices is only available to Education customers in North America, UK and Australia 4 )
Understand Web Usage 5
See what web content users are effectively focused on, as well as how often and for how long online tools are used, and identify if insecure or inappropriate content or websites are visited
Absolute Control Mobile App
Check the status of critical security controls on any device reported as lost or stolen, and freeze it immediately through the Absolute Control mobile app.
Google Play Store | Apple Store
2 Applications supported directly through the product: Endpoint Management (Microsoft SCCM, VMware Workspace ONE, Tanium, Citrix Workspace, Ivanti Endpoint Manager), VPN (Cisco AnyConnect, F5 BIG-IP Edge Client, Pulse Secure, Palo Alto GlobalProtect, Netskope), Endpoint Protection (Dell Advanced Threat Prevention, VMware Carbon Black Cloud, ESET Endpoint Antivirus, CrowdStrike Falcon, McAfee ePO, Ziften Zenith), and Data Protection (Microsoft BitLocker, Dell Encryption Enterprise, Dell Data Guardian, WinMagic SecureDoc Encryption). Any other application of your choice may be supported through a Professional Services engagement, which can be quoted upon request. Learn more
3 Only available on specific Lenovo devices.
4 Terms and Conditions apply. See FAQ for more details.
5 Only available for Chrome browser, on Windows and Chromebook devices.
LoJack for Laptops1 is a former product and brand. Device tracking andrecovery features are available for individuals via Absolute Home &Office, and for businesses/schools via the Absolute editions listed above.
1 LoJack® is a registeredtrademark of CalAMP.
Absolute's Persistence® is a patented security solution that providesa continuous, tamper-proof connection between devices, data, and the cloud-basedAbsolute console.
Lojack For Macbook Pro
Through our partnerships with device manufacturers such as Dell, HP, Lenovo andothers, Persistence is embedded in the firmware of computers, tablets, andsmartphones at the factory, remaining dormant until the Absolute agent is installed.Installation initiates a call to the Absolute Monitoring Center, and Persistence isactivated.
Once activated, the status of the Absolute agent or anythird-party applications is continuously monitored and, if it is missing or damaged,a reinstallation will automatically occur. Persistence will survive attempts todisable it, even if the device is re-imaged, the hard drive is replaced, or thefirmware is flashed.
Application Persistence is a feature of Absolute Resilience that provides embedded,self-healing capabilities to third-party endpoint controls, such as VPN, anti-virus,encryption, systems management, and other critical applications.
Virtually any app can be automatically reinstalled, regularly checked for versioncontrol & integrity, and IT teams alerted the moment anything abnormal occurs.
Application Persistence works with devices on or off yourcorporate network, and, as Persistence technology is embedded at the factory, itcan’t be compromised.
Lojack For Mac
Many organizations use Absolute to replace existing IT asset management tools andprocesses, and to supplement many popular security and device management solutions,such as Microsoft SCCM, Microsoft Intune, VMWare Workspace One, MobileIron, andmore.
Lojack Mac
Absolute can be used to report on the health of — andfill gaps in — these applications. Popular complementary features include:self-healing critical security controls, identifying sensitive data, and providingvisibility into devices not managed by other solutions.
Download the FullEdition Comparison Chart
View features for Chromebooksor Cloudbooks
View features by OperatingSystem
Absolute protects over 12,000 organizations worldwide
